Yesterday on the way back from a BRC meeting, I stopped in at Harvey to try and track down some interference we are getting on the 70cm repeater VK6RBY that is located on the scarp just east of the town. Listening on the input frequency 433.650 MHz the squelch was breaking as I entered the town limits. Within a few minutes of driving I’d tracked it down to a particular town block.
Yesterday on the way back from a BRC meeting, I stopped in at Harvey to try and track down some interference we are getting on the 70cm repeater VK6RBY that is located on the scarp just east of the town. Listening on the input frequency 433.650 MHz the squelch was breaking as I entered the town limits. Within a few minutes of driving I’d tracked it down to a particular town block.
I hopped out of my ute and tried to use the scanner to try and narrow it down further – without much luck. I’ll have to come back with a yagi to do any better. Since there seems to be a constant carrier with the occasional burst of pulsing, it’s probably a telemetry device of some sort.
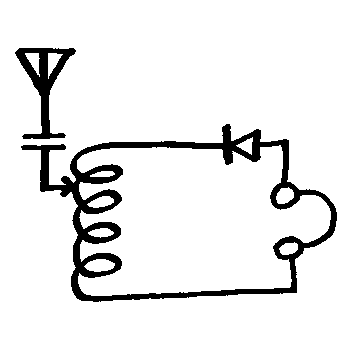
Interference to UHF amateur radio repeaters is a common issue, as the input frequencies in many countries overlap with the LIPD (low interference potential devices) band. In Australia LIPD devices are covered by a class licence that allows 433.05–434.79 MHz to be used with up to 25mW. Gadgets such as garage door openers and short range video senders are the types of transmitters in common use.
25mW is not much power, but standing on the side-walk near the source of the signal I could see the repeater tower, so it’s possible this is a legal device. However, plenty of higher powered devices, including telemetry transmitters can be found on eBay capable of transmitting between 100mW and 1400mW.
 As I was walking around with the scanner, I realised I hadn’t locked my ute, I pressed the lock button on the key fob and heard a chirp through the radio – clearly my Mazda key fob is a 433 MHz device. The chirp sounded like it might be some frequency shift keying (FSK), so I was keen to have a look at its spectrum. That seemed like a good job for my RTS-SDR dongle.
As I was walking around with the scanner, I realised I hadn’t locked my ute, I pressed the lock button on the key fob and heard a chirp through the radio – clearly my Mazda key fob is a 433 MHz device. The chirp sounded like it might be some frequency shift keying (FSK), so I was keen to have a look at its spectrum. That seemed like a good job for my RTS-SDR dongle.
 These little devices look like a USB thumb drive and can be had for about $10 on eBay.
These little devices look like a USB thumb drive and can be had for about $10 on eBay.
They are intended for watching digital TV on your laptop. Based on the RTL2832U and R820T chips, they are actually wide band VHF-UHF receivers.
Some smart hacker realised that the IQ output could be captured and processed and now there is open source software for most platforms so they can be used for radio fun. They are not high quality, and the output ends up with a few birdies and images, but if you want to take a quick look at a signal they are very handy.
Here is a screenshot of the software I use on the Mac – GQRX while the key fob is transmitting. The top part of the display is a Fast Fourier Transform (FFT) of the signal – basically a graph where the x axis is frequency and the y axis is the amplitude of the signal. The signal we are interested in is the two spikes in the centre. It clearly is FSK using two tones about 100 KHz apart. The bottom part of the screen is a waterfall display and you can just see the signal emerging.
The top part of the display is a Fast Fourier Transform (FFT) of the signal – basically a graph where the x axis is frequency and the y axis is the amplitude of the signal. The signal we are interested in is the two spikes in the centre. It clearly is FSK using two tones about 100 KHz apart. The bottom part of the screen is a waterfall display and you can just see the signal emerging.
Here’s a short video so you can see it in action.
I can’t see how to speed up the waterfall (to effectively stretch it out), if I could do that, we’d see the individual bits of the data being sent. Another approach would be to record the output as a WAV file (GQRX allows this) and process it to extract the timing of the high and low tones.
It would be possible to then transmit the code with an amateur UHF radio, but even if I had correctly decoded, and re-encoded the data this would be unlikely to unlock the car. These systems usually use some sort of rolling code (the code is different each time) to prevent this exact type of attack. In the rolling code system the receiver knows the next few codes the transmitter might send using an algorithm. Successful rolling code attacks generally rely on capturing a code at the same time as preventing its reception by the intended receiver – not a simple process if they are in range of each other.
If you haven’t got one of these RTS dongles, I highly recommend you grab one and have a play. It was nice to have it lying around when I needed it for this job, and you can’t beat the price.